🚨 Executive Summary: Deploying unbreakable mathematical provenance for Tier-1 defense logic.
C2I deepfakes destroy trusted origin analysis. The current paradigm restricts DDI from enforcing compliance because data lacks intrinsic memory.
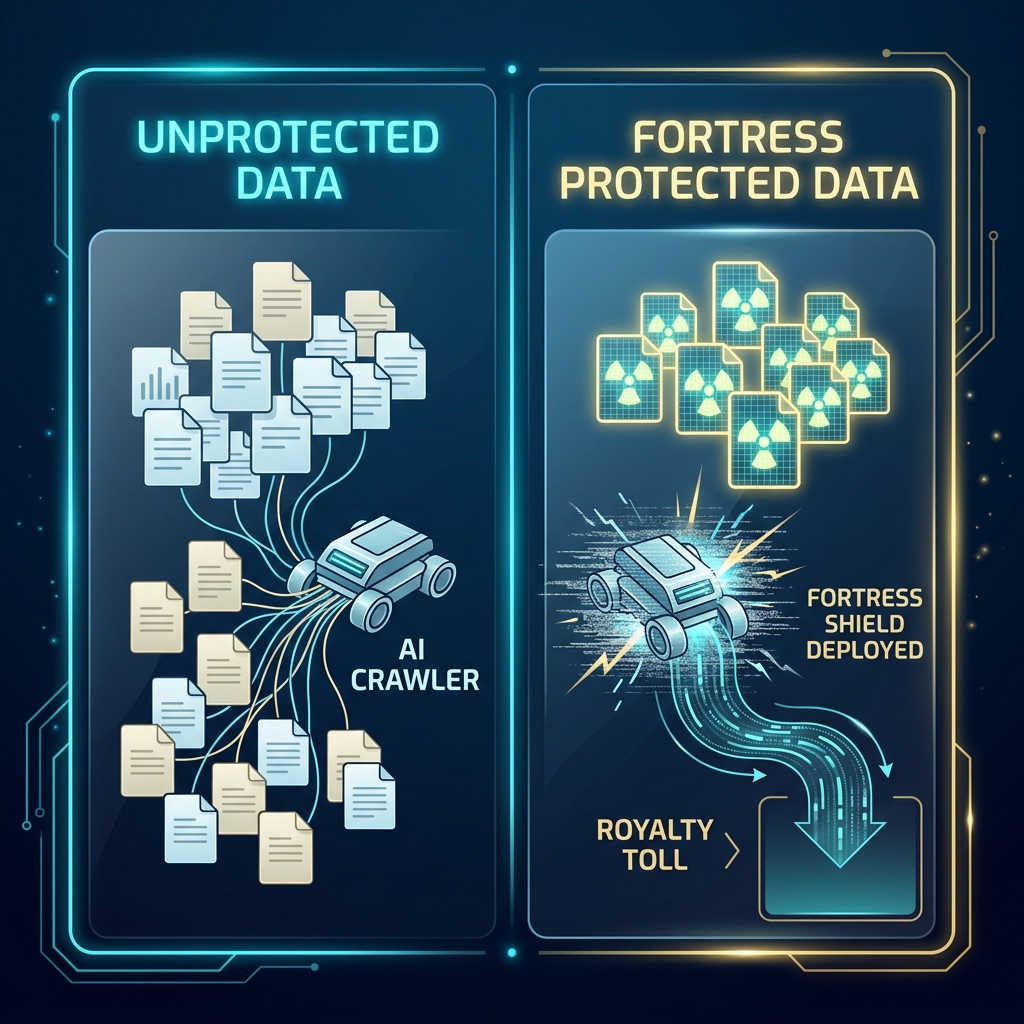
Sovereign proof of origin validating absolute truth. By utilizing DWT, we bypass the need for centralized DRM.