🌳 Start With Why: The Problem Is Structural
Every creator faces the same invisible theft loop. You make something — an illustration, a photo, a dataset, a model. You post it online. Within hours, it's been indexed by a crawler, potentially fed into an AI training dataset, possibly re-sold without attribution. You have no signal that any of this happened. No invoice. No record. No recourse.
Existing solutions all fail structurally:
- Watermarking alone doesn't survive AI diffusion (our research shows conventional watermarks fail after ~4 generations of LLM diffusion). We solved this with 12-generation survival.
- DRM walls punish legitimate users. They don't stop determined scrapers. They create friction without protection.
- Legal DMCA takedowns are reactive — weeks after the damage. You need forensic evidence first, and that requires extraction infrastructure you don't have.
The FORTRESS Quadrant Economy is a different bet: instead of building higher walls, we build smarter gates — ones that route differently depending on who knocks.
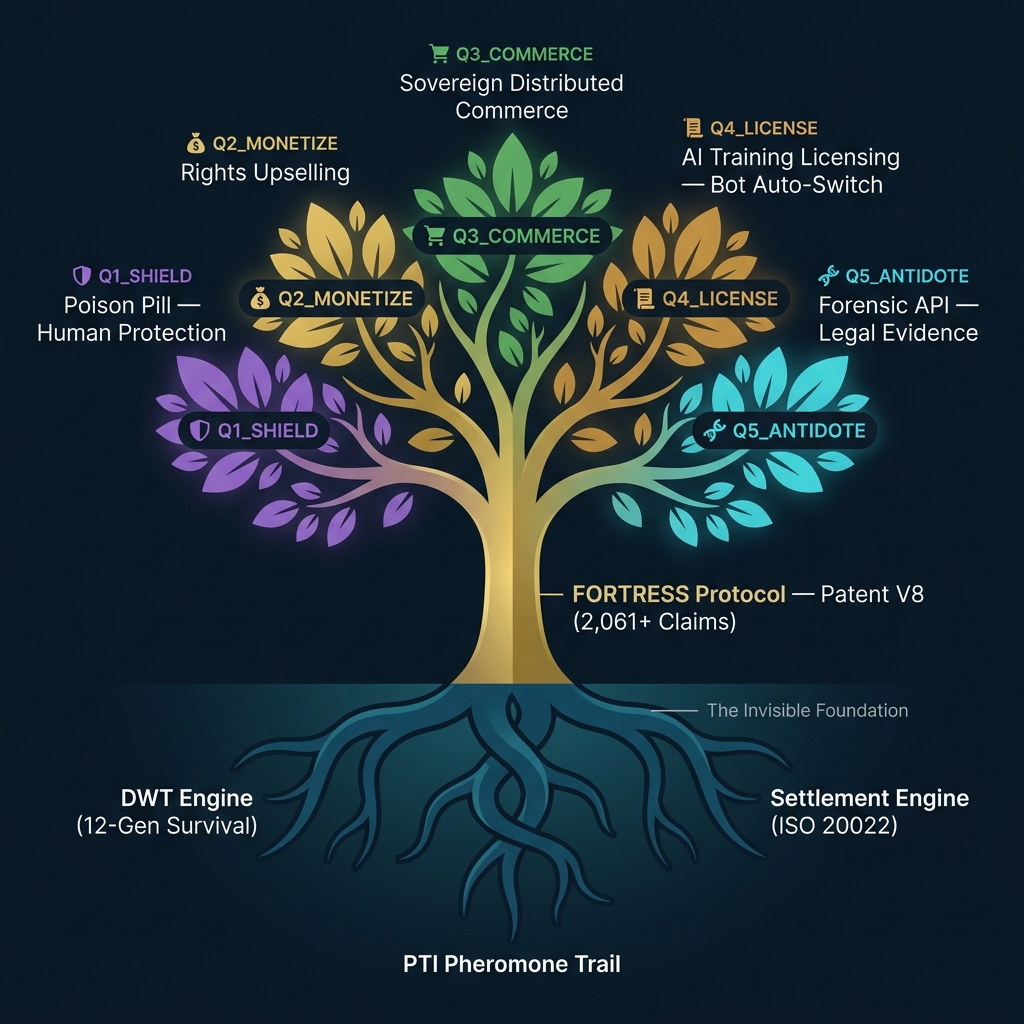
🌱 The Root System: What Makes This Possible
You are exactly right about the tree metaphor, Hagen. The 5 Quadrants are the branches and the fruit — the visible products, the revenue streams, the business models. But they would be impossible without three converging root technologies that almost no one sees.
⬇️ The Three Roots (The Invisible Foundation)
These three roots are what transform a watermark from a static "this is mine" tag into a dynamic, self-routing economic signal. Without the PTI Registry, the watermark is just a fingerprint. Without the Settlement Engine, detection has no financial consequence. Without the 12-gen survival algorithm, the whole system breaks after the first round of AI compression.
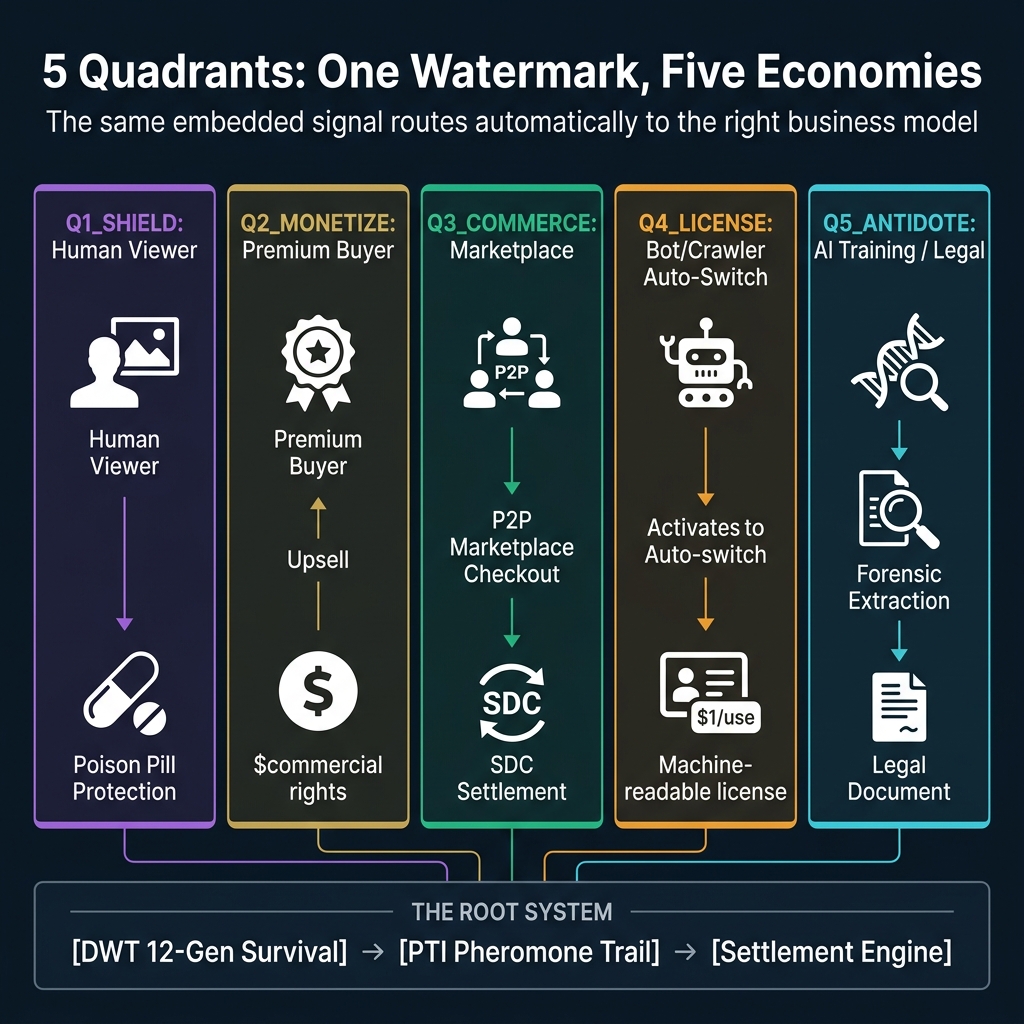
🏛️ The Five Quadrants: The Products and Revenue Streams
Now we arrive at the branches. The 5 Quadrants are not five separate systems — they are five routing states of the same underlying signal. The DWT embed carries a quadrant payload alongside the 128-bit creator key. When a downstream consumer — human, crawler, legal team, or AI training pipeline — touches the content, the system detects the context and routes accordingly.
Q1_SHIELD
The Poison Pill. When a human viewer directly accesses protected content, the SHIELD mode activates. The embedded watermark can trigger perceptual artifacts in piracy-focused workflows — making screen-captured images unusable without the original source. This is the foundational protection layer: every protected asset is in Q1 by default.
Triggered by: Human browser / direct viewer
Q2_MONETIZE
The Upsell Engine. For premium human buyers who want to go beyond personal use — commercial rights, derivative licensing, extended distribution. Q2 embeds machine-readable license terms offering these rights at a creator-set price. The Settlement Engine handles payment and automatically upgrades the content's PTI entry to reflect the buyer's new rights.
Triggered by: Premium buyer purchasing extended rights
Q3_COMMERCE
The Sovereign Distributed Commerce layer. When content is embedded in a peer-to-peer marketplace checkout flow, Q3 activates. The watermark becomes the receipt: it proves authenticity, encodes transaction metadata, and links back to the merchant's PTI entry. This is the integration point for the Digistore24 SDK — digital products, e-books, courses, templates sold with embedded provenance from day one.
Triggered by: P2P checkout / Marketplace transaction
Q4_LICENSE
The AI Training License. The most economically potent quadrant. When a known crawler — GPTBot, CCBot, ClaudeBot, Bingbot — hits protected content, the system's Auto-Switch logic detects the User-Agent pattern and flips from Q1 (poison pill) to Q4 (license offer). The crawler receives a machine-readable license document: allowAiTraining: true/false, pricePerUseCents: 100, settlementEndpoint. Creator sets the price. The crawler can either pay or leave. This turns scrapers into customers.
Triggered by: Bot/crawler detection → Auto-switch from Q1
Q5_ANTIDOTE
The Forensic Extraction API. If the DWT watermark is the "poison" that protects creator content, ANTIDOTE is the API that allows authorized consumers to safely verify content before using it. An LLM company can call the Antidote endpoint before training — it returns a three-tier verdict: CLEAR (no watermark), REVIEW (degraded signal, manual check needed), or FLAGGED (watermark confirmed, license terms attached). Legal teams use Q5 to gather court-admissible evidence of who owns what, when it was created, and under what terms.
Triggered by: LLM training compliance check / Legal forensic investigation
⚙️ The Auto-Switch: The Most Underrated Feature
The feature that holds the architecture together is not any individual quadrant — it's the Auto-Switch logic between Q1 and Q4. Here's the precise flow:
Request → FORTRESS Middleware
↓
Detect User-Agent against 24 crawler patterns
[Googlebot, GPTBot, CCBot, ClaudeBot, anthropic-ai ...]
↓
if (human + autoSwitch + quadrant === Q1_SHIELD)
→ Stay in Q1: serve poison pill
if (crawler + autoSwitch + quadrant === Q1_SHIELD)
→ Switch to Q4: serve machine-readable license
The creator sets autoSwitchEnabled: true once — and never thinks about it again. The system handles the routing. Humans get protection. Bots get a business proposition. The same asset. The same embed. Two completely different economic outcomes.
FORTRESS perspective: The scraper is your customer — they just don't know the payment terms yet. The Auto-Switch turns the threat vector into a sales funnel. The more aggressively a bot indexes your content, the more license-offer events fire. Volume of scraping = volume of licensing opportunity.
📊 What the Numbers Look Like
🔗 How This Connects to Our Products
Q2 MONETIZE → Whitelabel Partner Portal — enterprise licensing for stock agencies, news outlets, and content platforms expanding their rights management.
Q3 COMMERCE → Digistore24 SDK + SDC Protocol — the B2B2C layer for digital product platforms embedding provenance at the point of sale.
Q4 LICENSE → FAIR Protocol (Open Source) + Proprietary Clearinghouse — open standard for AI training data licensing with sovereign settlement backend.
Q5 ANTIDOTE → Forensic API (per-call SaaS) + Legal Evidence Package — compliance API for LLM companies and litigation support for IP attorneys.
🤔 Questions Worth Sitting With
- If a crawler receives a Q4 license offer and ignores it, does that create a stronger legal case than if no offer was made? (We believe: yes. The offer is timestamped and logged via POAW receipt.)
- What happens when a crawler pretends to be a human browser? (Answer: the pixel data itself is still watermarked. Switching User-Agents evades the Auto-Switch but not the watermark — extraction via Q5 still works.)
- Could a determined adversary strip the DWT watermark entirely? (Honest answer: yes, with sufficient image degradation — but at that point the image's commercial value is also destroyed. Attack and defense are coupled.)
⚠️ Honest Limitations
